3 Steps for Secure, Reliable Wireless Mobile Robot Networks
In a recent research study about robotics use across industry, Automation World found that 100% of the integrators responding to the survey have seen an uptick in interest for AMRs (autonomous mobile robots) among their clients over the past five years. In terms of real-world application of AMRs, 22% of end users responding to the survey say they are looking to implement AMRs in the very near term.
If you’re unfamiliar with AMRs, they are robotic carts that can navigate through an environment without the need for human guidance to carry a variety of materials between locations. AMRs are frequently replacing automated guided vehicles (AGVs), which were commonly used to automated movement of materials in the past. An AGV navigates by following wire strips or magnetic tracks along the floor. In contrast AMRs use a sensor technology called light detection and ranging (LiDAR) instead.
To build reliable connectivity platforms for AMR operation in warehouses and factories, fast and stable wireless connectivity is a fundamental requirement. The biggest challenge can be in determining how to build the right kind of wireless communications network.
Moxa, a supplier of edge connectivity, industrial computing, and network infrastructure technologies, recommends following three key steps to build robust communication networks for AMRs. These steps are also recommended for development of communications for automated storage/retrieval systems.
Step 1: Focus on industrial-grade designs
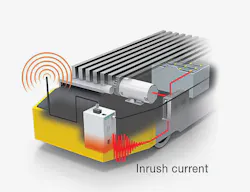
In any industrial application of wireless communication, electrical interference is an issue that must be addressed. This interference can stem from ground loops to the basic use of conveyor belts to move products. Also, the constant vibration created when an AMR is moving can also affect wireless performance.
Step 2: Deploy Seamless Wireless Connectivity
Wherever AMRs will be used, wireless roaming capability will be needed. According to Chuko, roaming technology enables wireless clients to constantly search for and switch to the nearest access point with the strongest signal before the wireless connection is lost.
Wi-Fi coverage can also impact the quality of wireless connections because it “determines how quickly the wireless device can identify nearby access points and thus roam more reliably,” he says. “Opting for wireless devices with MIMO (multiple-input and multiple-output) capability can further multiply the capacity of a radio link to enlarge Wi-Fi coverage. This also improves wireless performance and eliminates the need to install additional access points.”
Chuko also recommends determining if the wireless communication device you’re considering can be equipped with millisecond-level roaming technology and evaluating the use of external antennas for more flexible network deployment to achieve broader Wi-Fi coverage.
“You can use wireless sniffer tools within the area to trace various Wi-Fi spots to map out the actual profile of the radio coverage,” advises Chuko. “More often than not, you will need to fine-tune the network design after an on-site survey. Even when the Wi-Fi coverage is good and the RF signal is strong, you may not get good throughput. Physical obstacles, such as walls, may be preventing some access points and clients from ‘hearing’ each other, leading to a collision of Wi-Fi signals.”
Step 3. Look for built-in security and management software
Chuko cautions that even basic Wi-Fi network management tasks can pose cybersecurity risks. “For instance, if wireless clients can connect to access points without any authorization or authentication mechanism, this kind of unwarranted access may cause network breaches and even shut down the AMR system. That’s why we highly recommend securing all wireless communication devices after configuration and deny unauthorized devices access to the wireless network to create an additional layer of network security,” he says.
“Moxa has helped machine OEMs and system integrators worldwide to augment AMR and automated storage/retrieval systems for optimal reliability and efficiency,” he adds. “Moxa’s AP (access point)/bridge/client solutions combine a rugged design with high-performance Wi-Fi connectivity to deliver secure and reliable wireless connectivity. And with Moxa MXview network management software and AeroMag technology, customers can easily configure, manage, maintain, and troubleshoot their network.”