Is the Purdue Model Still Relevant?
Why this article is worth reading:
- Learn how industrial data flows have fundamentally changed with edge computing and cloud connectivity, where sensor data can now bypass traditional hierarchical structures to go directly from Level 0 to Level 5.
- Understand how this change is causing automation professionals to grapple with the fundamental challenge of how to balance the proven security and safety benefits of the traditional Purdue Model with the data accessibility demands of modern Industrial IoT and edge computing.
- Get insights on how to resolve this challenge with a hybrid approach that maintains the essential network segmentation and security protections while enabling the horizontal data flows that modern applications require.
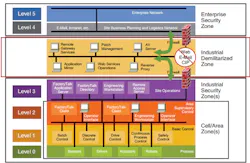
The well-known Purdue Model of Computer Integrated Manufacturing has become an iconic standard in the automation world for its industrial control systems architecture guidance. The Purdue Model has helped provide industrial communication security through its separation of layers and definition of how machines and processes should function and interact.
It quickly became so well accepted that it influenced the ISA-95 standard that defines the interface between enterprise and control systems. And its prescribed data flows have also helped keep industrial networks deterministic by ensuring that control networks are not overwhelmed with non-production data.
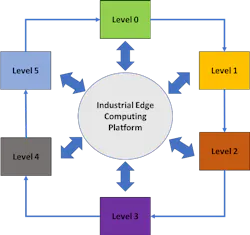
And with the use of edge computing devices becoming more common, “vast amounts of data can be collected at Level 1, processed, and sent directly to the cloud,” Shah says, thereby bypassing the hierarchical structure of data flows in the Purdue Model.
In modern, digitally connected control architectures, “there is no inherent need to funnel data up through different layers [of the Purdue Model],” says Shah. “Sensor data is being collected at Level 0 and sent to the cloud for predictive maintenance. And sending Level 0 data to Level 5 directly violates the segmentation aspects of the Purdue Model. Today, data can be derived from many sources and service many clients, opening up ever widening pathways for consumption.”
But scrapping the Purdue Model isn’t something Shah advises. “The Purdue Model still serves the segmentation requirements for both wireless and wired networks and protects the operational technology (OT) network from unwarranted traffic and exploits. These are key areas that need to be preserved to ensure the continuous flow of production and the safety of the workers operating the shop floor equipment.”
Instead, Shah advocates for a “hybrid solution that integrates into the Purdue Model to maintain segmentation for traditional instances of IT and OT data flow, but also provides the flexibility needed as Industrial IoT use cases become more prevalent and data becomes less hierarchical and more horizontal.
Around the outside of the new hybrid model diagram, the traditional Purdue Model data flows will continue to ensure throughput on the shop floor network is not comprised and maintain safe operation of shop floor equipment.
About the Author
David Greenfield, editor in chief
Editor in Chief

Leaders relevant to this article: