Process Automation: Making the Case for Integrated Safety
Process safety. Process or safety? Process and safety.
Process industries have debated for decades whether or not it makes sense to integrate control and safety functions. There are huge benefits to integration, but there are also challenges and concerns. The technology has advanced since the discussions that took place in the late ‘80s, and process automation is certainly able to better provide safety functionality today than it did then. But the debate isn’t over yet.
In an effort “to be pragmatic in how we approach the subject,” Luis Duran, product marketing manager for ABB, presented a case for integrating safety and process control during ABB’s Automation and Power World last week in Houston.
In the late 1980s, when Duran was working on one of his first process control systems, “process automation was not providing the functionality to do safety at that time,” he says. But it was still important to process plants to bring the information from the safety system into the process control. “We cannot be blind about what’s happening in the safety system.”
Safety standards dictate, however, that the basic process control system (BPCS) should be separate from the safety instrumented system (SIS). It’s the level of that separation that’s under debate. One camp is of the mind that no safety functionality should be performed in the BPCS at all. The other side says that “effective” separation rather than physical separation is enough to provide safety, while also offering the integration that’s beneficial.
No matter from which side you approach the issue, everybody has a shared interest in the importance of process safety. Whether in petrochemicals or upstream oil and gas, incidents are expensive, can hurt production and availability, and have a huge impact on human life. “At the end of the day, we want to make sure that we don’t have that impact—in the plant, or in the neighboring communities around the plant,” Duran says.
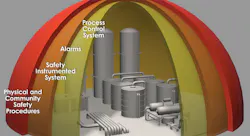
The way industry has dealt with the probability of such incidents is to install different protection layers, including the process control system, alarms, the SIS, and finally physical and community safety procedures. “The protection layers must be independent, not coordinated,” Duran says. “Any of these layers can fail at a given point of time. The other ones have to be able to respond independently from each other to keep the process safe. That’s how each of these layers can continue to work even though one of the layers has failed.”
But although the layers must be independent, that doesn’t mean they have to be uncoordinated, Duran adds. For operators to respond effectively to both normal and abnormal conditions, it’s important for them to have the information from both control and safety, while the technology ensures functional independence between the two.
Duran points to ABB’s 800xA High Integrity as an integrated process automation system with a safety component. Process control and safety run on different controllers, but share the same network. They also share the same operations interface and engineering, centralized historian and data archiving, and plant-wide sequence of events, as well as a common, integrated asset management strategy.
Duran argues that functional safety standards are performance-based; that the BPCS should be independent to the extent that the functional integrity of the SIS is not compromised, but physical separation might not be necessary. “The presumption is we’ve done it this way forever, but it’s not necessary,” he contends. Physical separation can of course provide the separation needed too, “but if you’re looking for integration, physical separation can cause a different kind of challenge.”
ARC Advisory Group lists some advantages of integrated safety and control as lower engineering and lifecycle costs, lower training and maintenance expenses, easier time synchronization, and improved asset and event management. However, they also list challenges: increased risk of common cause failures, the need for careful design to make sure that a BPCS failure does not affect the SIS, and greater management challenges.
The assumption is that you reduce common cause failures by having Company A do the process automation system and Company B do the safety system. “But even if you have systems from the same company, it is possible to analyze and reduce common cause failures in hardware, in software and then in the functionality and testing,” Duran says.
The potential common cause failures of a common structure can be analyzed and minimized during the system design to ensure that independence is maintained. “We use different technology sets working together to achieve not only the reliability but also to reduce potential human errors that can be introduced,” Duran says. “An independent third-party team verifies that the independence in functionality was achieved.”
Other advantages of an integrated system:
- Access control is a standard off-the-shelf feature, including write protection, bypassing and override mechanisms.
- Integrated testing is performed during the design validation and verification test, including network security.
- Version control, compatibility and interoperability testing are all part of the release procedure.
It’s important not to ignore the human element through all of this. All personnel involved with the safety system should be competent and follow procedures. “The safety certification of the controller is important,” Duran notes. “However, as important as those are, the human element—who gets to design the system and how the system is implemented—is even more important.”
According to a study called “Out of Control: Why Control Systems Go Wrong and How to Prevent Failure,” well over half of the incidents examined were built into the system before the system was even put in place—43 percent at the specification stage and 15 percent at design and implementation.
For the 800xA HI, features are built into system to prevent human error in design or implementation, Duran says. “By following the design practices that are publicly available, it’s possible to build robustness to integration and achieve independent protection layers,” he says. “People are key. All people involved in the safety system will have to have some degree of competence. Understanding functional safety is one of those competencies. Someone must demonstrate that competence.”
About the Author
Aaron Hand
Editor-in-Chief, ProFood World

Leaders relevant to this article: