Consolidated Monitoring: Risky Convenience or New Paradigm?
Remote monitoring is a fact of life. It is inherent in the logic of computer and networking technology—a fact that’s been obvious for some three decades since enterprising young engineers at Carnegie Mellon University networked their building’s Coke machine so they wouldn’t have to make the long trek from their offices only to find the machine empty or the Cokes warm. Industry initially lagged behind these Coke guzzling engineers, but eventually remote monitoring of individual components, machines or systems became commonplace.
Almost as soon as these point-to-point monitoring systems were installed, however, the relentless growth of computing power and networking technology generated new questions along with new capabilities: If you can monitor some of your key systems from across the plant floor, why not monitor multiple sites from the front office, or from anywhere in the world?
Such consolidated monitoring systems open the possibility of real-time production and equipment status data converging with higher-level systems like production planning and purchasing, as well as with key supplier systems. In addition to specific improvements in machine or process efficiency, this new level of integration, or convergence, is conjuring up visions of new ways of doing business.
As Harbor Research (Harbor Research, http://harborresearch.com) puts it in its recent Smart Systems Manifesto, “Beyond efficient support of products and equipment, the convergence of collaborative systems and machine communications will enable entirely new modes of services delivery and customer interactions. This implies a total paradigm shift. The depth of this shift has begun to suggest itself, but it is by no means accomplished.”
Diane Davis, director of product management, networking, for Red Lion Controls (Red Lion, http://www.redlion.net), concurs. “The industrial markets are in the early stages of enterprise-to-factory convergence,” notes Davis, adding, “The adoption of the connected factory is not being driven by specific industries as much as progressive companies that are leading the charge to become efficient. As a result, these companies are requiring more extensive monitoring of their processes and productivity.”
Managing the network
Along with opportunities, these expanded networks, with their need for more extensive monitoring and higher levels of data, bring a number of challenges. Setting aside, for a moment, questions involving best uses for this data, how do you manage the network itself? That’s a question Nick Sandoval, field application engineer for networking specialist Moxa Americas (Moxa, http://www.moxa.com), has spent plenty of time grappling with.
“A centralized monitoring and management system for the network is vital to ensuring network reliability,” Sandoval declares. “A managed network will be able to handle most problems, such as a downed link. But, should this happen, will you know of this mishap in a timely fashion? Not having a centralized monitoring system is like building a highway, and never surveying it. How do you know when there is a problem? When is there too much traffic? When do you have to expand?”
Sandoval says the most frequently employed solution is network management software (NMS). “This provides information that is important to all involved, not just IT. The industrial version of NMS is easier to read and diagnose than that most commonly seen in the IT space, yet it accomplishes the same goal—which is to monitor the status of the network and report any issues.”
NMS for the industrial space is designed to be intuitive and form a visual representation of the network, Sandoval says. Most are also standards-based, thus easing interaction between multiple vendors.
“An NMS is the easiest way to permit people from different disciplines to monitor a network,” Sandoval maintains. “Moxa’s MxView, for example, is web-based, thus anyone in an organization can simply use their web browser to access it. This approach brings a commonplace IT technology to the hands of plant floor engineers.”
However, there are times when central management can be either distributed or accomplished by using a solution other than an NMS. Many factories are now moving from unmanaged to managed Ethernet switches, says Sandoval. Each deployed managed switch provides new network monitoring data points for feedback on data traffic and the health of the network.
“This allows someone to use an HMI to communicate directly with a switch, permitting the SCADA to monitor the network and make decisions based on the network health,” says Sandoval. “For example, if the network becomes too busy, unessential poll traffic can be dialed back. If there are failures in the network, it can trigger a watchdog timer that can put drives and motors to a safe state.”
There is, of course, another aspect to network management: managing the wealth of data generated by centralized monitoring. “As data extends beyond process control, and the volume of data collected from multiple locations increases, the ability to prioritize and reliably deliver critical data will become more challenging,” observes Red Lion’s Davis.
Taking a page from Red Lion’s own playbook, Davis adds that networking products that provide a communication layer for reliable data transmission and include features like quality of service (QoS) help prioritize data within the network.
Enlisting the experts
Another approach to the problem of data management is to let the experts do it for you. As Harbor Research notes, the remote monitoring of a specific machine is now increasingly being done by equipment OEMs as a value-added service. In addition, some of the major names in automation, like GE Intelligent Platforms (GE Intelligent Platforms, http://www.ge-ip.com), Siemens (Siemens, http://www.siemens.com/entry/cc/en) and Bosch (Bosch, http://www.bosch.com), now offer what Harbor calls “compound applications” for monitoring.
These systems differ, but their common denominator is that they allow companies to offload monitoring for entire functions or classes of assets within a plant, or across plants. These systems can manage equipment, analyze the data they collect, integrate that data with the company’s enterprise system, and in some cases make decisions based on that information.
“These types of services are especially valuable for smaller customers who don’t always have the infrastructure to monitor all this,” says Steve Pavlosky, general manager, solutions ecosystems, for GE Intelligent Platforms, “particularly as Baby Boomers retire, taking with them expertise that is often hard to replace.”
GE Intelligent Platforms has introduced Equipment Insight into this space. As part of GE-IP’s Proficy suite of automation solutions, Equipment Insight enables OEMs to securely collect data from connected machines, analyze that data, and get actionable information to people to deliver better service levels and optimize asset performance and profitability.
“Today’s OEMs are being pressed to deliver higher levels of service to customers without increasing cost,” continues Pavlosky. “Most are looking to monitor their equipment and share asset information with their end users, but many don’t have the resources to do it effectively. For some, this solution can provide a new business model that can bring them closer to their customers by providing a service the customer needs.”
GE Intelligent Platforms customer TempuTech Inc. (TempuTech, http://www.temputech.com) recently put such a system to the test to serve its customers. To help farmers and grain management companies protect their investments, TempuTech developed two software offerings—a temperature monitoring system and a hazard monitoring system. The temperature monitoring system sends standardized temperature reports to customers daily so they can reduce the grain temperature as needed to protect grain from hot spots caused by infestation and germination. These hot spots can cause the product to combust. The company’s hazard monitoring systems pinpoint problems in grain conveyor systems such as belt misalignments, slippage, speed variation and overheated bearings.
TempuTech teamed with GE Intelligent Platforms to integrate the systems and offer real-time, proactive alarming, automatic backup and redundancy features, mobile capability, customizable reports, and in-depth data on alarms. Equipment Insight from GE gathers and analyzes temperature and hazard data from TempuTech customers and activates alarms in response to specific incidents and conditions, helping TempuTech proactively notify its customers.
TempuTech can now dispatch the nearest technician to the customer, with the right parts and tools in-hand, thus improving utilization of its field-service resources.
As a pilot, TempuTech installed Equipment Insight to run the hazard monitoring system at a large grain company. The GE system allows onsite viewing, virtual monitoring via a secure Cloud environment from mobile devices or browsers, and control of grain transfer operations across the facility. In addition to the local HMI hardwired screens, the virtual monitoring is provided via a dedicated, secure Cloud-based environment, combining the redundancy and security of a physical connection with the convenience of the Cloud. Preliminary indications are that the Equipment Insight solution will improve the grain company’s asset performance, reduce unplanned downtime, and improve decision-making effectiveness.
TempuTech plans to install a temperature monitoring system at one of the grain company’s other facilities to remotely monitor its plant’s 5,000 temperature sensors. “Virtually centralizing unlike applications, devices and sensors via a web-based remote monitoring and diagnostic solution is improving our ability to service this account, enhancing our value to them as a vendor and reducing our overall costs-to-serve,” notes Adrian Merrill, vice president of operations for TempuTech.
Next step: TempuTech will offer a system that controls all aspects of a grain storage facility, combining different applications, devices, sensors, databases and systems into one mobile-accessible system that can start, monitor and stop key processes, and create preventative maintenance reports.
Security: The 800-pound gorilla
Clearly, consolidated monitoring offers a host of benefits today, and the promise of more in the future. Focusing on one aspect of this new environment, the mobile app, Janice Abel, principal consultant for research firm ARC Advisory Group (ARC Advisory Group, http://www.arcweb.com), states that “the app is just the beginning of the new industrial revolution, with functionality that leverages and builds upon other mobile capabilities.” Harbor Research sees this new environment as an example of “interacting in new and creative ways,” and believes these “collaborative networks” herald the beginning of a new paradigm.
Heady talk, but the 800-pound gorilla in the room remains security. “Network security was not a concern when manufacturing facilities operated in separate bubbles,” observes Red Lion’s Davis. Today, however, with networks open to outside vendors and smartphones, security is very much on the front burner.
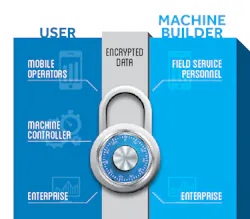
Like many other large vendors, GE Intelligent Platforms is extremely aware of the problem. Matthew Wells, general manager, automation software, summarizes the company’s approach this way: “Security is an ever-evolving challenge. We have created a very secure solution. People are concerned about the connections between the control network and the Cloud. We create a secure tunnel, with certificates that provide a high level of encryption. Also, we conduct security seminars for our developers, in addition to ongoing monitoring of threats. To aid our customers in this respect, we contracted with a third party to create a secure deployment guide.”
Davis summarizes Red Lion’s best practices this way: “Network expansion into the field is most easily accomplished by using industrial routers to provide secure, reliable high-speed communication.”
Before making investments in these industrial routers, there are some key factors to keep in mind, says Davis. “Some wired routers utilize virtual private networks (VPNs) to securely extend the private (corporate) network to remote locations, like factory floors,” she says. “Companies should look for products that allow the use of IPSEC and OpenVPN, each of which offers unique VPN features for different network applications. IPSEC uses robust encryption and shared parameters to secure data traffic from the head end to remote assets. OpenVPN utilizes shared certificates to ensure data security while providing secure data transmissions between routers.”
Davis advises that the next layer of security should be a firewall that uses stateful packet inspection (SPI). The SPI process scans individual packets of data and approves or denies each packet based on known services that are currently running. For instance, a remote site may only be allowed to transmit Modbus data packets to limit the use of data required. In this case, any non-Modbus data would be rejected by firewall in the router.
“Similar to a firewall, which approves or denies data packets, routers should also offer an access control list (ACL),” Davis says. “An ACL is a list of approved or denied user credentials that allow or deny users from accessing the cellular device. Coupling an ACL with user-level authentication adds security by only allowing certain services to be accessed by specified users.”
Finally, as GE’s Wells mentioned, be cognizant of the fact that the security environment is always evolving, so continuous threat assessment is a necessity.