Although the term machine-to-machine (M2M) didn’t really come into play until the past five years or so, for considerably longer companies have been working on sharing data from one machine to another. Now more than ever, process industries are gathering mountains of sensor data, and need a better way to reliably and securely move that data to a central location, notes Ashish Sharma, CMO of FreeWave Technologies.
FreeWave, which has been working on M2M solutions since the early ‘90s, today announced a wireless broadband platform that expands its capabilities, extending enterprise and IT networks all the way from the field. This week at the International Wireless Communications Expo (IWCE) in Las Vegas, the company announced WavePoint, a versatile high-speed wireless networking platform that securely communicates industrial data over long distances to enable M2M broadband and SCADA applications.
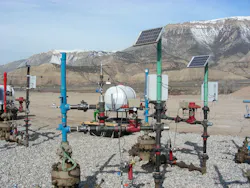
Expanding on FreeWave’s narrowband long-range technologies, WavePoint is designed to meet the challenges of integrating difficult-to-reach field locations by providing powerful wireless IP routing capabilities combined with a choice of frequencies and network deployment capabilities for any application. Users can extend broadband connectivity to remote locations from a unified platform.
The device supports any network infrastructure, including four radio frequencies (900 MHz, 2.4 GHz and 5 GHz ISM, and U-NII bands) and options for 3G and Wi-Fi. It can support up to four wireless OFDM broadband modules per unit.
WavePoint incorporates several technologies that let customers deploy it in a number of ways— wired network access, cellular network backhaul, local area communications, high-speed backbone communications, Wi-Fi hotspot access, and mobile mesh networking—all through a single platform.
With support for four different radio frequencies, FreeWave can help its customers choose the right frequency for the right application—one frequency for Wi-Fi access, SCADA communication on another, backhaul on another. It also enables a cellular backhaul wherever there’s a cellular infrastructure available. “There are built-in software mechanisms to be able to, in a smart way, enable a cell backhaul if the 5GHz frequency goes down,” Sharma says. “So mission-critical data is not lost. This gives them a lot of different capabilities from what they have seen before.”
Traditionally, communications might primarily deploy wireless networks for only narrowband sensor data, Sharma adds. “They don’t do a Wi-Fi hotspot, and they don’t do video surveillance. In a lot of cases, they use T1 links, paying lot of monthly charges for that, just to get a few megabit per second throughput.
WavePoint can support any network infrastructure, enable remote video access, empower multiple Ethernet and serial devices simultaneously, and eliminate (or consolidate) telecom access circuits (T-1/E-1 and DS3), and device integration is truly plug-and-play.
In one example, a customer was using T1 circuits and “paying tons of money,” Sharma says. “At two different locations, they were able to take the T1 circuits out. They got much more bandwidth, and now they’ve got their own network that they can rely on rather than working with telcos to lease their capacity.”
Since a single WavePoint platform enables multi-purpose communications and can operate in multiple frequencies, customers can easily integrate it with existing local area networks (LANs), wide area networks (WANs) and more, protecting their existing network infrastructure investments. The platform is also secure, defending against unauthorized access using security protocols based on the Advanced Encryption Standard (AES). It complies with today’s IT-centric security policies, and can extend corporate IT networks to remote and difficult-to-reach locations.