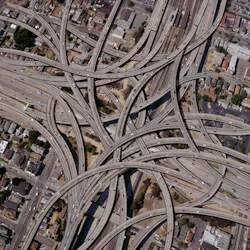
Calling it one of the greatest public works projects of all time, Mark Wylie talked this morning about the U.S. interstate highway system. Touching all of our lives in one way or another, it was successful largely because of the infrastructure that it established. It brought standardized routes, provided connections from city to city, created improved security and control, gave routing options—all kinds of infrastructure changes that made it easier to travel from one place to another and helped the country’s economy to grow.
Rather than just providing a history lesson on the impact of Dwight Eisenhower’s presidency on American life in the 1950s and beyond, Wylie was actually likening the federal interstates to an industrial Ethernet infrastructure, with similar mechanisms used to control traffic and provide security. In charge of the industrial Ethernet infrastructure program at Belden, he gave an opening session at the company’s Industrial Ethernet Infrastructure Design Seminar in Houston this week.
Like our country’s interstate system, industrial Ethernet is best organized into smaller road segments (subnets or VLANs), providing various routes to connect manufacturing to the enterprise, and controlling traffic for security and performance capabilities. Wylie urged seminar attendees to move away from the confusion of ad hoc networks that he compared to the smaller roads of pre-interstate travel, and instead move data through a more efficient Ethernet arrangement.
Wylie detailed 12 best practices for industrial Ethernet infrastructure design:
1. Segment communications into groups (subnet). There are several ways you can break down your network into groups, but however you do it, segmenting will make it easier to grow your network in a more orderly fashion. One way is to create a subnet for each geographical area of your plant—each manufacturing line, each shipping line, the control room, etc.
“Devices on the same subnet can talk to each other very easily,” Wylie said. “As a rule of thumb, 80 percent of the traffic will stay in the subnet.”
2. Segment communications into groups (VLAN). A virtual LAN is another way to divide your network, and a logical way to make this split might be across devices performing a similar function, such as tying all the cameras together. Again, about 80 percent of the traffic will typically stay within the VLAN, Wylie said.
3. Create a network infrastructure—connecting to the enterprise (IT). “All the data you have doesn’t do any good if you don’t get it up to the enterprise level itself,” Wylie said, explaining the importance of using high-speed, high-throughput switches for the backbone; less expensive Layer 2 switches inside a subnet to connect devices; and Layer 3 switches (routers) to connect physical groups (subnets) together.
4. Consider Power over Ethernet (PoE). Though using Power over Ethernet requires that you have a switch that supports PoE, the benefit that it provides power and communications to devices through one cable.
5. Specify traffic control for performance. “Know the amount of data that you’re going to be sending upstream,” Wylie said. “Choose a managed switch that has the capabilities we talked about.”
Quality of service (QoS) prioritizes traffic and evens things out so no one source grabs all the bandwidth, he noted. Also, tools like IGMP Snooping and Querier can properly handle broadcast and multicast traffic.
6. Get switches with proper IP ratings. IP ratings describe a device’s protection against solids and liquids to ensure switches will survive in the environment in which they’ll be used.
7. Security. Much like the interstates have marked entrances and exits, the same can be done to add security to networks, Wylie said. It’s important to start with a risk assessment, understanding your vulnerabilities. Configuring subnets is a good initial step, then configuring VLANs is another. “You also have to enable security features in switches and routers,” Wylie said. “If you have a port that isn’t being used, turn it off.”
Add firewalls to protect perimeters, zones and remote access. “It all becomes a consideration with defense in depth,” Wylie said, including policies and procedures, physical security, network security, computer security and device security.
8. Redundancy. Again drawing a parallel with the interstate system, Wylie talked about two routes to go through or around a city, just as I-495 is an alternate route to I-95, taking a wider berth around Boston. Similarly, you can architect your network so you have duplicate switches talking to the same device.
Evaluate your redundancy needs by identifying the largest needs for uptime, and ranking and assessing the impact if that area were to fail.
9. Environment. This area encompasses corrosiveness, industrial protocols, electrical noise and temperature extremes. Add any additional standards, specifications or concerns to make sure you’re choosing the right switch.
10. Cables, cordsets, connectors. Key considerations include copper vs. fiber based on distances and necessary data rates, for example. You’ll also need to consider how much flexing the cable will be subjected to. Also, you can choose to hardwire everything in the field, or you can connectorize.
11. Network management tools. These will give you the “ability to see your network and map what’s going on and get status from your network real time,” Wylie said. “Being able to configure everything that’s in the network is a critical step.”
12. Infrastructure lifecycle needs. Get a project checklist to think about how you will install and maintain your system.
“There are more than 46,000 miles of highways that cross the country that make it easier to do our jobs. It’s the same thing for industrial Ethernet infrastructure,” Wylie said in conclusion. “It’s important to think about these 12 best practices as you lay out that system.”