Control System Cybersecurity in Action
If there was one theme that seemed to dominate the agenda at the Siemens Automation Summit 2014, it was cybersecurity. On the first day of the event, I sat in on three different cybersecurity-related sessions. Industrial control system (ICS) cybersecurity experts from Dow Corning and DuPont presented two of these sessions.
DuPont’s Top-Down/Bottom-Up Approach
Eric Feldmeyer is manufacturing technology senior engineer at DuPont who has worked with automation and process controls for 30 years. The last three years he has been focused on industrial control system (ICS) cybersecurity for DuPont.
Complying with the Department of Homeland Security’s CFATS RBPS8, ISA 99 and IEC62443 are overburdening the already stretched process control engineer, said Feldmeyer. With DuPont approaching ICS cybersecurity from a top-down design and bottom-up implementation approach, Feldmeyer’s task has been to address the top-down/bottom-up gap and ease the process for the control engineers.
An important aspect of closing this gap, according to Feldmeyer, is to choose a corporate leader for the projects who has access to corporate leadership, can express ideas clearly, knows the process control network and working parameters, and knows cybersecurity. You also need to choose a plant/site leader, he says, who can manage multiple tasks, has access to plant leadership and knows process control systems. As you can see here, the connective tissue between the two sides of the gap is knowledge of the process control systems.
Having the corporate approach to cybersecurity outlined, but no specific corporate cybersecurity project yet authorized, Feldmeyer said the two leaders (corporate and plant) at DuPont “used resources via influence” to address the company’s cybersecurity issues. This approach developed during their visit to the first site targeted for ICS cybersecurity implementation; here they outlined the existing gaps and developed a plan with site controls experts and the IT group. “We used Microsoft Project to track the process over the four months we worked at the site to close gaps,” he said.
According to Feldmeyer, the principal, ongoing action items for engineers at the site are to sustain the cybersecurity activities implemented in the process, follow the standards outlined, and stay current and connected to corporate cybersecurity programs.
There is a need for constant communication between the plant and IT teams, said Feldemeyer, which DuPont facilitates via quarterly meetings with the process control group, a monthly steering team meeting with management, and periodic meetings over the course of the year with regional leaders and plant managers. The corporate IT and site security teams also focus on staying in alignment with global regulations, monitoring industry trends around cybersecurity, and following U.S. CERT incident response reports.
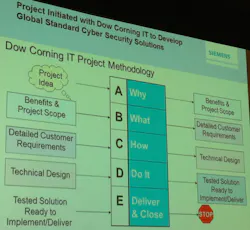
Dow Corning’s IT & Process Control Connection
As associate process automation consultant in Dow Corning’s Global Manufacturing Automation team, Charlie Stibitz is on the front lines of Dow Corning’s ICS cybersecurity operations. He notes that the company’s formal cybersecurity plans are of a relatively recent vintage, having started in earnest in 2011 when Dow Corning standardized its process control operations around the use of Siemens PCS 7 controllers.
“Before 2011, Dow had local control teams in charge of control system use and, as a result, had 32 different control systems installed,” he said. “We now have a global automation team in place and have completed more than 40 PCS 7 controls systems projects.”
Along with controller standardization, the Dow Corning automation team is also working with corporate IT to develop a global cybersecurity approach. This initiative, by its nature, is ongoing—but a great deal of headway has already been made, according to Stibitz.
A key aspect of Dow Corning’s approach to ICS cybersecurity involves referencing the Simatic PCS 7 Compendium F as a best practice benchmark. “This industrial security configuration manual covers plant and network security and system integrity from a defense-in-depth approach, notes Stibitz. “It covers zoning and separating by firewalls, system hardening, and host protection with whitelisting and user admin and operator permissions, as well as patch management, antivirus, backup procedures, remote access, definitions, and abbreviations.”
Stibitz noted that Siemens PCS 7 Compendium F came in handy “because IT and process automation have different policies for system requirements, and we needed a unified approach to cybersecurity design, roles, responsibilities, and policies between the two groups.”
One of Dow Corning’s ICS cybersecurity approaches involves managing access to shared systems via Active Directory. “Only a few Active Directory experts have access to the entire structure using a special account, which is not intended for daily use,” said Stibitz. “Plus, only PCS 7 engineers can add/delete PCS7 groups or create/modify policies for PCS 7 computers. Changes or additions to user policies are reviewed and tested by both IT and PCS 7 administrators.”
All PCS 7 systems at Dow Corning are behind firewalls and have separate patch management policies, Stibitz said.
About the Author
David Greenfield, editor in chief
Editor in Chief

Leaders relevant to this article: