ISA99 Committee Advances Cybersecurity Standards
The ISA99 committee on industrial automation and control system (IACS) cybersecurity has primary responsibility for developing the ISA/IEC 62443 series of standards on this subject. The committee recently held a series of working meetings in Frankfurt, Germany, to assess the current status of the standards and confirm plans for future work. This included discussions related to several of the fundamental concepts that form the basis for the ISA 62443 series of standards.
Several documents in the 62443 series have been formally published or are about to be released to the committee for comment or vote. Recent publications include 62443-2-3, Patch Management in the IACS Environment; and 62443-2-4, Requirements for IACS Solutions Providers. Documents that have recently been circulated for review and comment include 62443-4-1, Product Development Requirements; and 62443-4-2, Technical Security Requirements for IACS Components. Finally, the following draft documents will soon be issued to the committee for review and approval: 62443-1-3, System Security Metrics; and 62443-3-2, Security Risk Assessment and System Design.
Several fundamental concepts form the basis for the 62443 series. The second edition of the 62443-1-1 standard will introduce each concept, which will be further detailed and applied in the remaining standards in the series.
Over the course of the Frankfurt meetings, those present reviewed several of these concepts and reaffirmed their importance as key elements of the series. Any inconsistencies across the standards were noted and will be addressed in subsequent editions.
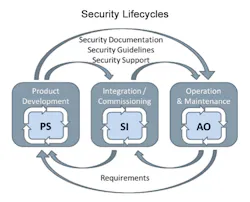
The design, development, implementation and operation of industrial control systems take place in the context of intersecting lifecycles, each addressing a specific set of activities and involving particular contributors. The product development lifecycle is primarily the responsibility of the product or system supplier. Integration and commissioning are the focus of system integrators. Operation and maintenance are the responsibility of the asset owner. Collectively, these lifecycles provide the context for gathering the requirements and subsequently developing secure products, systems and solutions.
Applying the zones and conduits concept is an essential first step in risk assessment and system design. The 62443-3-2 standard on this subject will soon be circulated to the committee for review and approval, with review by the broader IEC community to follow soon after.
In addition to the above established concepts, members also discussed several topics that are still evolving:
Metrics. The committee recently began to develop a set of metrics that could be used to assess progress against many aspects of the standards. This material will appear in the form of the 62443-1-3 document.
Protection levels. There was a proposal to define protection levels to provide additional guidance on the application of the standards. This proposal was developed by a group that has been working with the German National Committee and is being offered to the ISA99 committee for use in the 62443 series. There was consensus that this subject should be assigned to a new task group for further development.
Risk assessment. Risk assessment is also an important element of an effective cybersecurity management system. Attendees reviewed and discussed a proposed methodology included in the current draft of the 62443-3-2 standard. Additional comments and feedback will be collected as part of the formal review and comment process.
The stakeholder community for the 62443 standards on IACS security include suppliers, integrators and asset owners across a broad range of industries. Each of these groups has different levels of interest in and applicability for the various types of standards in the series.
Those interested in learning more about the information contained in the 62443 standards will soon have available several new drafts for review and comments, as well as completed and published standards and reports in areas such as risk assessment and patch management.
These standards can be applied now to design, configure, operate and maintain industrial control systems. Application assistance is available in the form of a series of training courses available from ISA. As the full set of normative requirements and informative guidance becomes available, the committee’s attention will begin to shift to develop additional tools such as metrics and use cases.
>> Eric Cosman, [email protected], a consultant for ARC Advisory Group, has more than 35 years of experience developing, delivering, managing and supporting operations IT solutions in the process industries. Assignments and responsibilities have included process automation systems development, communications network design, functional and technical architecture design, and technology lifecycle management. He recently retired as an operations IT consulting engineer with Dow Chemical.
About the Author
Eric C. Cosman
Consultant, ARC Advisory Group

Leaders relevant to this article: