Note to Management: Cybersecurity Is Your Responsibility
“We stand on the brink of a technological revolution that will fundamentally alter the way we live, work, and relate to one another. In its scale, scope, and complexity, the transformation will be unlike anything humankind has experienced before... The First Industrial Revolution used water and steam power to mechanize production. The Second used electric power to create mass production. The Third used electronics and information technology to automate production. Now a Fourth Industrial Revolution is building on the Third, the digital revolution that has been occurring since the middle of the last century. It is characterized by a fusion of technologies that is blurring the lines between the physical, digital, and biological spheres.”
–Klaus Schwab, Founder & Executive Chairman, World Economic Forum-14 January 2016
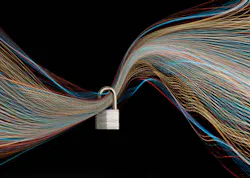
As the Fourth Industrial Revolution to which Klaus Schwab refers gathers momentum and the lines between physical and digital grow increasingly blurred, the issue of cybersecurity has become a key concern. In the wake of recent global ransomware attacks, there is a growing realization that cybersecurity is everyone’s responsibility, not just an IT issue. Consequently, some companies are scrambling to bolster their cybersecurity defenses, gain operational cyber risk and remediation intelligence, and train operations managers in the art of cyber self-defense.
But the reaction is far from universal. “Cybersecurity is an understandable concern and continued education is needed for end users and OEMs to become comfortable with continuous data exchange and analysis,” notes PMMI in its just completed report, “The Evolution of Automation.” (For complete study, go to pwgo.to/3040). Based on interviews with 60 end users, OEMs, technology suppliers, and “industry experts,” the report suggests that while a majority (58%) of information technology (IT) and operational technology (OT) departments are working together, a substantial minority (42%) of those interviewed say either OT/IT collaboration is not happening, they’re not sure if it’s happening, or if it is happening, the process “needs improvement” (see image at top of this article).
Recent technological advancements are drawing manufacturing operations managers into realms far beyond the traditional packaging and processing technologies, including such things as autonomous robots, 3D printing (additive manufacturing), interconnected sensors, smart phones, and GPS devices that are touchpoints on the Internet of Things. The Fourth Industrial Revolution, or Industry 4.0, finds today’s managers coping with systems that operate in near “dark factory” autonomy. Gone are the days when any clickety-clacking packaging line could be serviced by any one of the team of operators it took to run the machine, so long as the operator had a wrench.
Transformation is coming
The Fourth Industrial Revolution, says Dr. Schwab, “is disrupting almost every industry in every country. And the breadth and depth of these changes herald the transformation of entire systems of production, management, and governance.” Unfortunately, the May 12th and June 27th global ransomware attacks that infected upwards of 400,000 business and government computer networks in more than 60 countries are one negative consequence of the evolving manufacturing landscape. The understandable fear of operations managers is that the two attacks—which exploited operating system vulnerabilities, encrypted mission-critical data, and shut down production lines—won’t be the last, leaving neither large nor small packaged goods manufacturers unscathed.
In the wake of the May 12 and June 27 ransomware attacks, hundreds of companies, governments, healthcare institutions, and manufacturing operations around the world were privately assessing the impact of the malware intrusions on their operations. A few companies went public after they were attacked:
• Seven days after the June 27th virus hit, global confectionery manufacturer Mondelez International was putting as good a face as one could expect on the cyberattack that reportedly disrupted shipping and invoicing during the last four days of the second quarter and cut three percentage points from its second-quarter sales growth. Mondelez said it was “making good progress in restoring our systems across the enterprise. Since the time of the incident, our teams have done remarkable work to continue to operate the business, manufacture our products, serve customer needs and progress the recovery activities. We believe the issue has been contained and a critical majority of the affected systems are up and running again.”
• At Reckitt Benckiser (RB), CEO Rakesh Kapoor said the “force of this virus was very significant.” An RB statement said the attack disrupted “the company’s ability to manufacture and distribute products to customers in multiple markets across the RB Group. “Consequently,” the company reported, “we were unable to ship and invoice some orders to customers prior to the close of the quarter.”
• Approximately half of reported cyberattacks are against companies with $50 million in revenue or less, according to a Bloomberg BNA report www.bna.com/small-business-cybersecurity-n73014462316/ on testimony presented to the Small Business Committee of the U.S. House of Representatives. The $50 million revenue level includes most packaging and processing machinery makers and a number of container and material vendors as well.
Both the May and June cyberattacks exploited vulnerabilities in Microsoft’s Windows operating system—vulnerabilities for which Microsoft had issued security patches months earlier.
The cyberattacks taught operations technology (OT) managers and their information technology (IT) peers one overarching lesson: To repel and recover from cyberattacks, OT and IT management must collaborate more closely, update network software frequently, and deploy Windows system patches as soon as they are available. That lesson is now being appreciated by senior company leaders as critical to their business survival and growth.
Help is on the way
Fortunately, just as packagers, processors, and technology vendors seek cybersecurity help, they’re getting it from a surprising source: an insurance broker who’s been operating in the advanced manufacturing space for several years and has now put a cyber intelligence swat team in place to support those operations. That broker is AHT Insurance, a specialist in traditional liability insurance for the advanced manufacturing sector. Now the firm, where George Forrester is Director of Manufacturing Practice, is expanding its offerings to add a suite of cyber risk reduction services to its platform of physical safety and risk reduction insurance.
In putting together this cybersecurity risk remediation portfolio of services, which it calls Ensconce, AHT has assembled a collaborative offering of compliance assessments, legal consultation, and specifically tailored insurance solutions for packaging and processing professionals. It’s as unique an approach as the threats that are faced by the industry sectors that AHT serves.
The Ensconce risk management platform comprises individuals and boutique organizations with specific experience in the packaging and processing sectors. Participants include IoT solutions provider ei3 Corp., industrial automation systems integrator PHD Technology Solutions, cyber security consultants, incident response providers, and attorneys, coupled with what AHT calls “a responsive and customized insurance solution as a means of additional risk transfer.”
“The key differentiator and motivation behind the Ensconce platform is the implementation of proactive loss control measures, with insurance as a final risk transfer method,” says Brendan Rooney, Cyber Practice Leader at AHT. This is done so that in the event of an incident, clients are prepared to respond to a compromise of their industrial control systems or plant floor operations.
Traditional cyber insurance products that focus on middle market manufacturers offer an approach that is more reactive than proactive, says Rooney. Such insurance products typically rely on pre-selected panels to provide remediation services after losses have occurred. “This,” says Rooney, “can be problematic because downtime of any length resulting from an operational compromise means lost opportunities and reduced profits, not to mention contractual violations and additional damages.” Additionally, he notes, “pre-selected panelists don’t always have the necessary packaging and processing experience to make insightful evaluations.”
AHT’s Ensconce approach begins with a “scoping call” to determine what controls the packager or processor has in place. This is followed by a third-party assessment from one of AHT’s selected network security experts, which include BorderHawk and The Crypsis Group, two pre-breach preparation providers and consultants. Next, the consultants call on outside legal counsel—specialists in network security and its impact in the legal environment as it applies in the advanced manufacturing industry—to discuss compliance requirements outlined in a variety of regulations and frameworks on network security. Chief among these is “Framework for Improving Critical Infrastructure Cybersecurity,” a set of industry standards and best practices developed by an industry/government collaboration and published by the National Institute of Standards and Technology (NIST) “to help organizations manage cybersecurity risks.” (pwgo.to/3029)
This process is followed by recommendations and remedial measures that can be undertaken by clients to ensure that they are making themselves a difficult target for would-be attackers.
“If you want to put a percentage on it,” says Rooney, the Ensconce strategy “is 90 percent avoidance/mitigation and 10 percent insurance. As new threats emerge in cybersecurity, the Ensconce job is to make sure that our clients are as prepared as possible for these events. Simply purchasing insurance is not a sustainable risk transfer method if that is the only protection that you are affording yourself as an organization. Cyber risk remediation insurance is new and the market is evolving as losses are incurred, so insurance in this market is more for balance sheet protection than it is for actual remediation of an incident.”
By coupling insurance with a conscious effort on a layered “defense in-depth” strategy, says Rooney, “packaging and processing professionals will be far more prepared to deal with potential incidents and can continue to harness the benefits of connected machinery through operational efficiency.”
Editor's note: Packaging World is published by PMMI Media Group, which also publishes Automation World. PMMI Media Group is owned by PMMI, The Association for Packaging and Processing Technologies.
About the Author
Ben Miyares
Contributing Editor, Packaging World

Leaders relevant to this article: